BLOG
MSF6
MSF (Metasploit) version 6. Network possible detection ? OJ ( @TheColonial ) is a clever guy and a main contributor to the open source project of Metasploit. One of MSF6’s goal is to get rid of Strings in order to fly even lower … so close to the ground...to avoid any...
Lsass Minidump file seen as Malicious by McAfee AV
The other day, I was shadowing a colleague of me who was doing a red team. The client was running McAfee AV. While the reputation of that AV isn't the best, it got a bit in the way for a few minutes. After doing a lateral movement, my colleague was doing a procdump of...
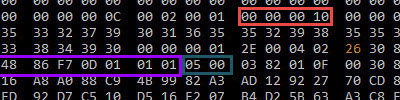
Meterpreter reverse_http how does it communicate ? between device and the MSF (part 1)
Before reading note: for practical reasons (time consuming) not all the printscreen shots have been made with same settings (ip addresses mainly i used once 192.168.150.196 and sometimes 192.168.1.71) For tests i created a simple reverse_http meterpreter build with...
Cortex XDR components
cyvrfsfd.sys : Palo Alto Networks cyvrlpc.sys : Palo Alto Networks tedrdrv.sys : Palo Alto Networks cyvrmtgn.sys : Palo Alto Networks cyverak.sys : cyvera, Palo Alto Networks tedrpers-7.???.sys : Palo Alto Networks cyinjct.dll : Palo Alto Networks ntnativeapi.dll :...
WFP shenanigans, can we abuse WFP to block EDR telemetry and alerting ?
Last few days, I've been playing with the WFP componant of Windows. WFP = Windows Filtering platform Many informations blogs are existing like the great one from Pavel who really deeped dive into it which I recommand to read...
WEC Part 2
This is under construction Commands to troubleshoot your WEC/WEF Forwardings PS Code to get status of the Listener winrm e winrm/config/listener PS Code to get status of a Forwarding Channel wecutil gr Security Above we see only one Active source forwarding it's logs...
WEC Part 3
Step 2.1 : Kibana Download latest release of Kibana here : https://www.elastic.co/cn/downloads/kibana It's a large zip file. Extract the zip file to C:\Program Files Run a CMD as Admin cd "C:\Program Files\kibana-7.14.1-windows-x86_64\" start in interactive with :...
Top 10 easiest way to Harden your Windows Domain
The following 10 quick wins, will not prevent you to be full 100% hack proof, but I promiss you, if you are able to implement those 10 things, then a hacker will have much more trouble to become a Domain Admin user from a simple User, to deploy it's Ransomware or...
ADCS DFIR Forensic ESC1-7 attacks
Summary While there isn’t anything necessarily inherently insecure about AD CS (except for ESC8 as detailed below), it is surprisingly easy to misconfigure its various elements, resulting in ways for unelevated users to escalate in the domain. Personnally I...