Updated on 2 Nov 2021 with new SentinelOne version 21.6.2.272
A very small little post, of a little experiment I did in my lab.
I’ve used the nice and interesting code of Ausurusrex ( https://github.com/asaurusrex/Probatorum-EDR-Userland-Hook-Checker ) which is a C++ code that will show you all the functions that are hooked by your EDR.
Then I modified it a little bit, to accept loading a DLL.
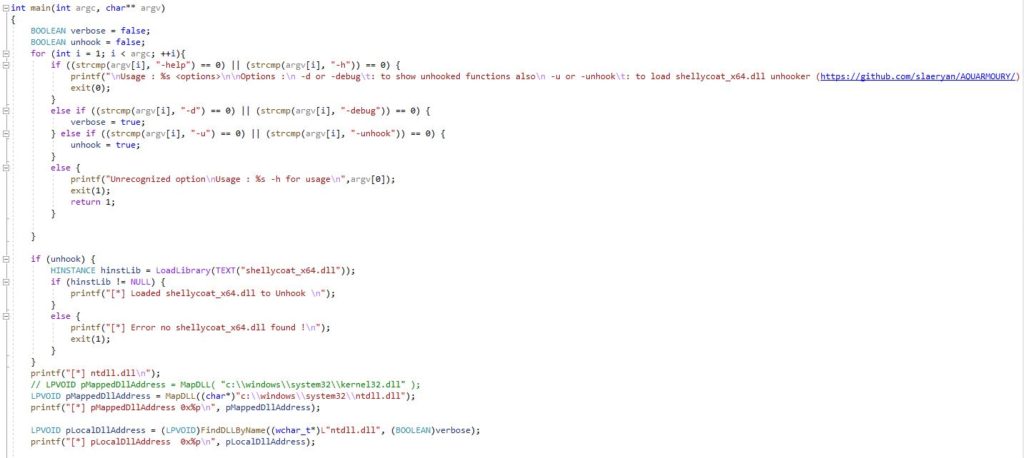
Then I compiled @Slaeryan AQUARMOURY shellycoat unhooking dll ( https://github.com/slaeryan/AQUARMOURY )
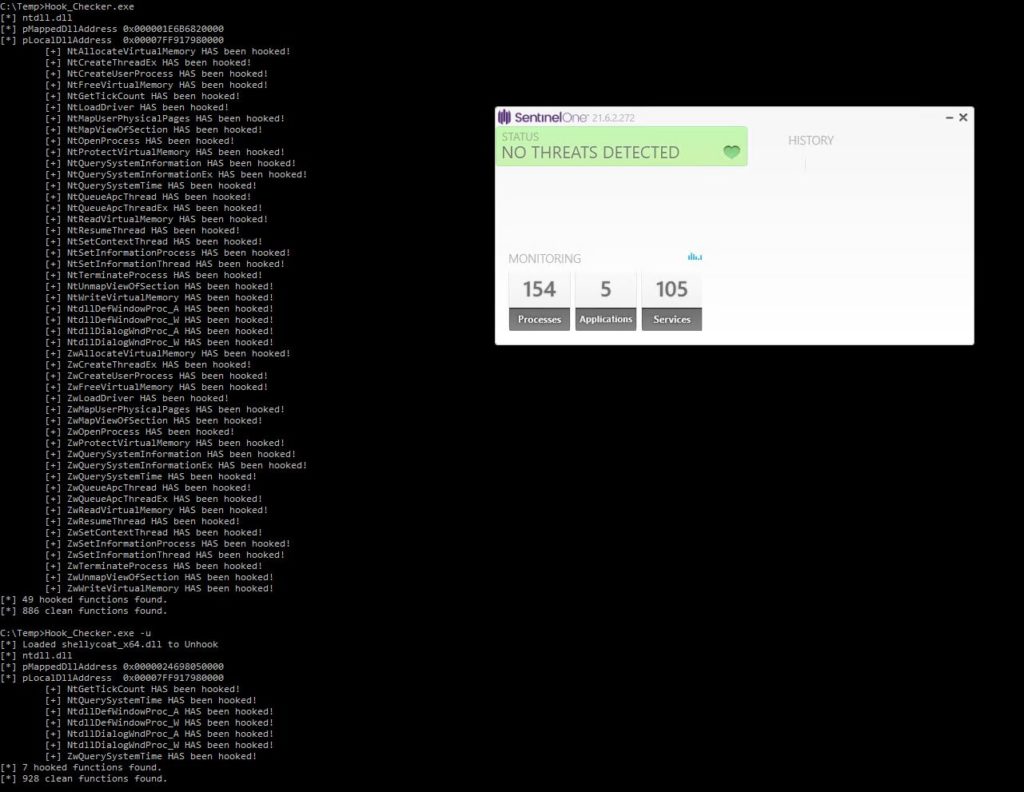
Here is my result under a SentinelOne which uses Userland Hooking.
Test 1 : 42 Functions are hooked in ntdll.dll by SentinelOne (49 but 7 are already detected even do they are not see README of Hook_Checker)
Test 2 : All functions have been unhooked in ntdll.dll by loading the disposable shellycoat dll ! Nice 🙂
Next ?
I was wandering why some EDR we couldn’t see the hook. Like Cortex XDR and Ensilo (FortiEDR).
The answer is simple. The hooks are Kernel based.
Thanks to @MrUn1k0d3r who kindly answered some of my questions and he published the hooks of XDR here : https://github.com/Mr-Un1k0d3r/EDRs/blob/main/cortex.txt
So why sometimes unhooking isn’t enough ?
So if the theory was complete. If my executable unhooked SentinelOne in Userland I should be able to run procdump or any other LSASS dumper tool.
Why does it fail ?
Next Article here <=
References :
https://github.com/asaurusrex/Probatorum-EDR-Userland-Hook-Checker by Asaurusrex and shared by netbiosX
my modified version here : https://github.com/k4nfr3/Probatorum-EDR-Userland-Hook-Checker/
https://github.com/slaeryan/AQUARMOURY from @Slaeryan
You can also use hook_finder from Mr-Un1k0d3r : https://github.com/Mr-Un1k0d3r/EDRs
0
So this unhooking doesn’t seem to do much anymore with the latest S1 client (21.5.3.235) – it says it’s unhooked but S1 is still picking up on everything – any idea?
Hi,
thanks for your feedback. I don’t know this version … as the current version are around 4.4 which is nothing to do with version 25 ??? Is this comment just a prank because there is frustration on showing how easily it is bypassed ? Anyway, as long as the hooks are Userland, you will be able to see them. Other products moved from UserLand hooking to Kernel hooking. Which is the case for Cortex XDR, and FortiEDR and then … it’s impossible to unhook except if you go through Kernel level yourself.
I finally took the time to update to a newer version. 21.6. And I still have the exact same behaviour
Everything is very open with a very clear explanation of the issues.
It was really informative. Your website is very helpful. Many
thanks for sharing!
Hello there! I could have sworn I’ve been to this web site before but after
browsing through many of the articles I realized it’s new
to me. Anyways, I’m certainly happy I came across it and I’ll be bookmarking it and checking back frequently!
Great post! We are linking to this particularly great post on our site.
Keep up the great writing.